QoS priority marking is the practice of labeling network traffic so switches, routers, firewalls, and wireless systems can recognize which packets should receive better treatment when the network becomes busy. In voice networks, this usually means marking real-time media and call-control traffic so delay-sensitive packets are less likely to be stuck behind large file transfers, software updates, backup traffic, or bulk cloud synchronization.
That distinction matters because voice quality is shaped by timing. A phone call can tolerate a little packet loss, but it becomes noticeably worse when latency rises, jitter becomes unstable, or packets arrive too late to be useful. QoS priority marking helps network equipment identify which traffic needs fast, predictable forwarding and which traffic can wait a little longer.
In practical deployments, QoS priority marking is often one part of a larger voice optimization strategy. A well-designed network still needs enough bandwidth, stable switching, proper VLAN design, sensible trust boundaries, and appropriate queueing policies. Marking by itself does not fix congestion, but it gives the rest of the QoS system the information it needs to make better forwarding decisions.

QoS priority marking helps network devices recognize voice traffic early so real-time packets can be handled with lower delay and more predictable forwarding behavior.
What QoS Priority Marking Means in a Voice Network
Marking is a label, not the whole QoS policy
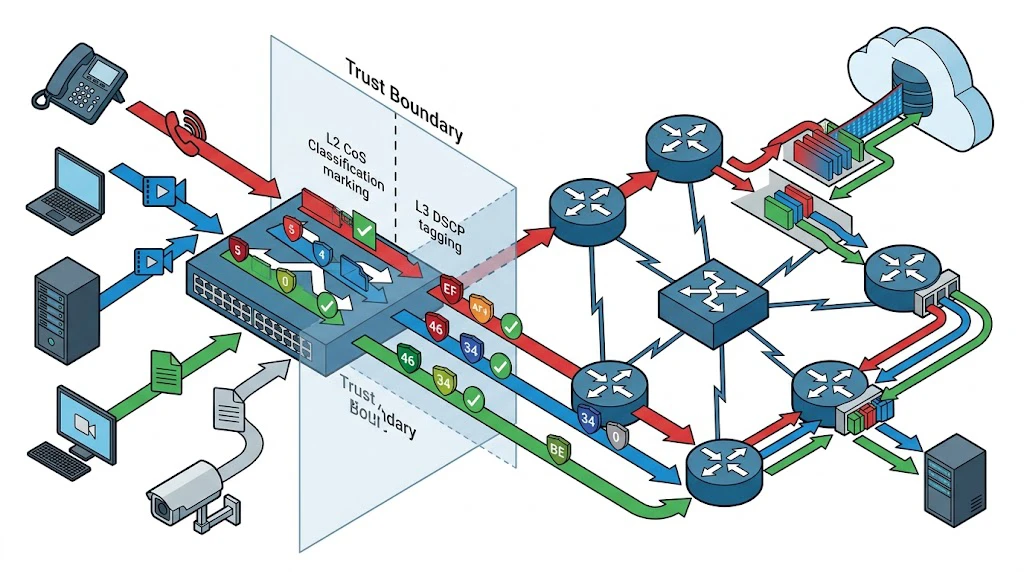
Many people use the phrase QoS as if it were one single feature, but in real networks it is a chain of related actions. Traffic is first identified and classified. After that, packets can be marked with a priority value. Only then do downstream devices know whether those packets should be placed into a priority queue, shaped, policed, or protected during congestion.
That is why QoS priority marking should be understood as an instruction attached to traffic, not as the complete optimization process. A packet marked correctly but ignored by the next switch gains little benefit. On the other hand, a well-marked packet traveling through a network that trusts and honors that marking can receive much better treatment end to end.
Why voice traffic needs special handling
Voice packets are small, frequent, and time-sensitive. A large software download may use more bandwidth, but it can tolerate short pauses and retransmissions. Voice cannot. If too many voice packets are delayed in the same path, users hear robotic audio, clipped speech, long mouth-to-ear delay, or broken sentences.
For this reason, voice bearer traffic is commonly separated from general application traffic. In many enterprise designs, the speech media itself is marked with a high-priority DSCP value, while call signaling traffic receives a different but still important marking. This allows the network to keep the actual conversation moving quickly while also preserving reliable setup and teardown of calls.
How QoS Priority Marking Works
DSCP marking at Layer 3
At the IP layer, QoS priority marking is usually done with DSCP values in the Differentiated Services field. These values tell routers and Layer 3 devices how packets should be handled across the network. In voice environments, the best-known recommendation is to mark telephony media with EF, which corresponds to DSCP 46.
EF does not magically reserve bandwidth on its own. Instead, it signals that the traffic belongs to a low-delay, low-jitter treatment class. When network policies are built correctly, EF-marked packets are directed into appropriate low-latency queues or strict-priority mechanisms so voice media can cross congested links with less disruption.
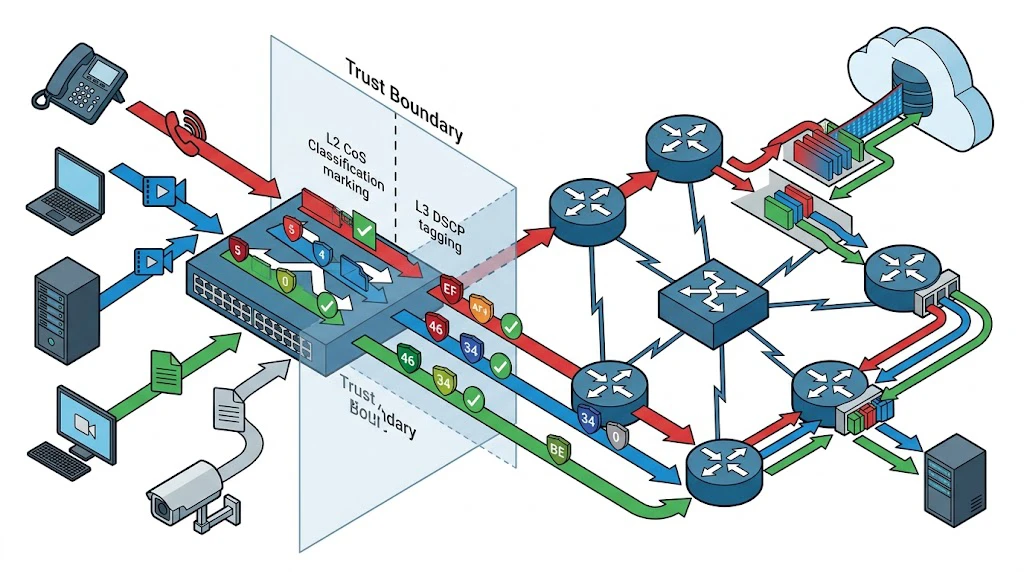
CoS and 802.1p marking at Layer 2
Within switched Ethernet domains, traffic may also be marked using Class of Service values carried in 802.1Q tags. This is often called 802.1p priority marking. In many IP telephony environments, voice traffic is associated with CoS 5 on the access layer. That gives switches an immediate Layer 2 indication that the packet should be treated as high priority.
Layer 2 marking is especially useful between the IP phone and the first switch, because it helps the access switch sort traffic before routing decisions are even involved. From there, the switch may preserve the original marking, translate it into a Layer 3 DSCP value, or remark it according to campus or WAN policy.
Trust boundaries and remarking behavior
A trust boundary is the point in the network where devices decide whether to accept an incoming marking or overwrite it. This matters because not every endpoint should be allowed to declare its own packets as mission-critical. If a laptop or unmanaged device can mark any upload as top priority, the QoS design quickly becomes meaningless.
In voice deployments, the network often trusts markings from known IP phones while applying stricter rules to PCs connected behind them. Some switches use CDP or LLDP-MED awareness to identify a phone port, trust the phone's voice marking, and classify workstation traffic separately. This design keeps the network from being both overly permissive and unnecessarily rigid.
The access-layer trust boundary is one of the most important decisions in voice QoS design because it determines which markings are preserved and which are rewritten.
Common Marking Values Used for Voice Optimization
Voice bearer traffic
The actual speech stream carried over RTP is usually given the highest practical forwarding priority among enterprise user applications. In many standards-based voice designs, this traffic is marked with DSCP EF. In Layer 2 switched segments, it is often associated with CoS 5. This pairing is familiar because it gives both switches and routers a consistent signal that the packet belongs to a low-latency service class.
The goal is not to make voice consume unlimited bandwidth. In fact, voice priority queues are typically controlled carefully to prevent starvation of other traffic classes. The purpose of high-priority marking is to protect a relatively small but highly delay-sensitive stream, not to let every real-time application dominate the network.
Call signaling traffic
Voice signaling traffic such as SIP messages, call setup exchanges, registration events, and related call-control protocols is also important, but it usually does not need the same forwarding treatment as the audio stream itself. Many enterprise QoS models place signaling in a separate class such as CS3 so it remains protected without competing directly with the speech media queue.
This distinction is helpful during busy periods. If voice signaling were treated exactly like bearer media, control messages and RTP could be mixed too aggressively in the same priority path. By separating them, the network can protect call setup and control reliability while still giving the most time-sensitive queue to the actual audio packets.
Management and best-effort traffic
Not every packet from a voice device should be treated as premium traffic. Web management sessions, firmware downloads, analytics uploads, and routine background communications may belong in lower classes. Good QoS policy is selective. It identifies what truly needs optimized delivery and avoids marking everything at the same high priority.
That restraint is one of the marks of a mature design. When all traffic is high priority, nothing is. Clear differentiation between media, signaling, management, and generic data gives the network room to make useful decisions under load.
Deployment Benefits in Real Voice Networks
Improved call consistency during congestion
The most obvious benefit of correct priority marking is more stable voice quality when the network is busy. Users are less likely to experience stutter, clipped syllables, or long conversational pauses during peak traffic periods. This is especially valuable on shared WAN links, uplinks between crowded floors, and sites where voice, video, surveillance, and normal business traffic all traverse the same infrastructure.
In branch deployments, this can make the difference between a system that sounds reliable every day and one that seems fine only when the network is quiet. Priority marking does not remove the need for capacity planning, but it improves resilience when temporary contention appears.
Better interoperability across multi-vendor networks
Standards-based marking practices make life easier when IP phones, switches, routers, wireless systems, SBCs, gateways, and WAN services come from different vendors. A consistent DSCP and CoS design helps preserve voice intent across those boundaries. That is one reason standards-oriented traffic classes remain useful even when the hardware estate is mixed.
Without a shared marking model, one device may label packets correctly while another silently remaps them into a different class. The result can be subtle and frustrating: calls work, but performance fluctuates because the network is no longer treating media and signaling the way the designer intended.
Faster troubleshooting and cleaner policy design
Priority marking also improves visibility. When packets are classified clearly, administrators can inspect captures, interface counters, QoS policies, and queue statistics to see whether voice traffic is being handled as expected. This shortens troubleshooting time and makes it easier to separate a bandwidth problem from a marking problem, or a queueing problem from an endpoint misconfiguration issue.
Over time, that clarity helps teams build more maintainable voice policies. Instead of treating every performance complaint as a mystery, engineers can trace how traffic was marked, whether it was trusted, how it was queued, and where it may have been altered.
Consistent priority marking makes voice performance easier to monitor because administrators can correlate packet markings, queue behavior, and user experience more directly.
Where QoS Priority Marking Is Commonly Used
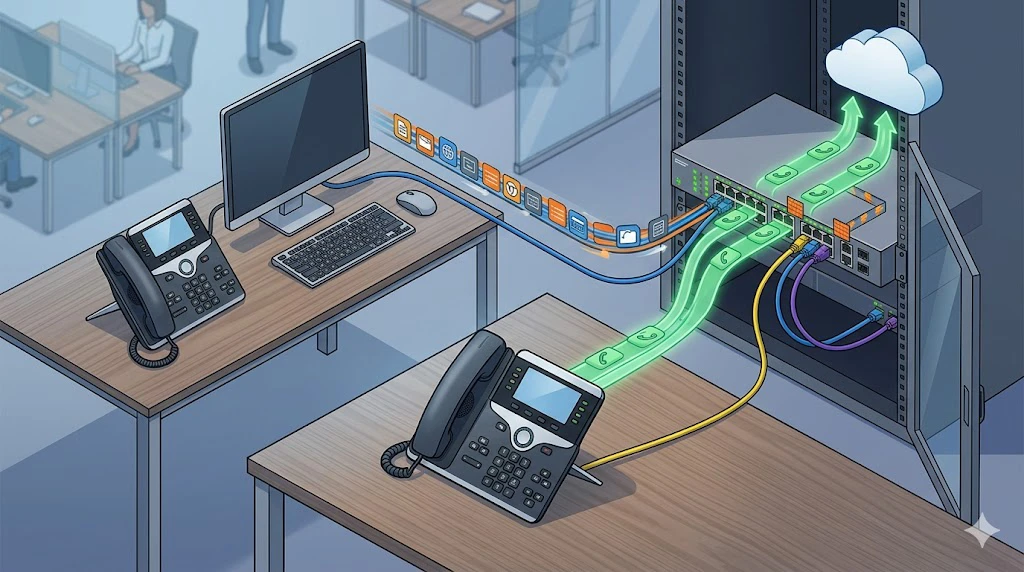
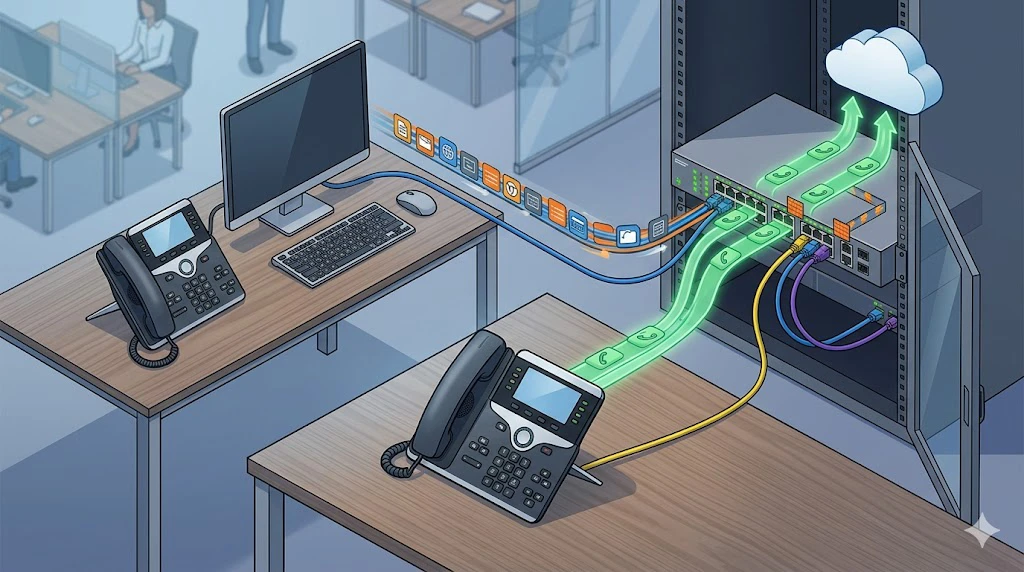
IP phones and enterprise PBX networks
In office voice systems, IP phones commonly mark speech and signaling traffic so campus switches and routed uplinks can process them correctly. This is one of the most familiar QoS use cases because the call flow is predictable and the business expectation for call quality is high. IP PBX platforms, SIP servers, and voice gateways all benefit when the network honors those markings consistently.
These environments also highlight why access-layer configuration matters. The phone may mark packets correctly, but the switch still needs the right trust state, VLAN design, queueing policy, and uplink behavior to preserve those benefits beyond the desk port.
SIP trunks, WAN links, and branch voice networks
QoS priority marking becomes even more valuable when voice leaves the local LAN and crosses limited uplinks or service-provider handoffs. Branch routers often classify and preserve marked media toward data centers, hosted PBX platforms, or SIP trunk providers. On slower links, queueing and shaping policies work best when marked traffic arrives in a clearly defined class.
In these scenarios, correct marking helps voice compete fairly against cloud backups, software distribution, video traffic, and normal business application flows. It also gives administrators a repeatable policy model across many sites instead of forcing each branch to behave differently.
Paging, intercom, and emergency communication systems
Voice optimization is not limited to desk phones. SIP paging systems, IP intercom terminals, emergency help points, industrial telephones, and command-and-dispatch endpoints also benefit from predictable treatment. These systems may not always carry constant traffic, but when they are used, the audio path often needs immediate, intelligible delivery.
That is why priority marking is relevant in transportation, campuses, industrial sites, healthcare facilities, and public safety support environments. A paging broadcast or emergency call that arrives late or distorted can be more than a nuisance. In some settings, it affects coordination, safety, and response speed.
Implementation Considerations and Common Mistakes
Do not rely on marking alone
One of the most common mistakes is assuming that because packets are marked EF or CoS 5, the problem is solved. It is not. Markings still have to be trusted, preserved, and mapped into the correct queues. If an uplink is oversubscribed and no low-latency queue exists, the tags alone will not protect the call.
That is why proper voice optimization combines marking with queueing, scheduling, capacity planning, and policy verification. Good design treats marking as the start of the conversation, not the end.
Watch for remarking at boundaries
Traffic often changes behavior at routing boundaries, WAN edges, firewalls, SD-WAN overlays, Wi-Fi controllers, cloud edges, and service-provider handoffs. Some devices preserve DSCP, some rewrite it, and some strip or ignore it unless configured carefully. A voice flow can therefore leave the phone correctly marked and arrive at the WAN in a weaker class than expected.
That is why end-to-end validation matters. Teams should verify not only what the phone sends, but also what the access switch trusts, what the router queues, and what the WAN provider actually honors. A policy that looks correct in one interface view may still fail in the full path.
Avoid over-marking the network
Another mistake is marking too much traffic as critical. If media, signaling, video, management, backups, and application syncs are all labeled with premium priority, the queue loses meaning. Over-marking can harm the very traffic the policy was meant to protect.
Strong QoS design is disciplined. It reserves high-priority treatment for traffic that truly depends on low delay and low jitter, and it assigns other traffic to suitable classes based on business value and technical sensitivity.
Conclusion
QoS priority marking is one of the most practical tools for improving real-time voice performance on a shared IP network. It gives the network a reliable way to recognize speech media, call signaling, and related traffic classes before congestion turns a minor delay into a user-facing audio problem.
Its real value appears when it is part of a complete voice strategy: correct endpoint marking, sensible trust boundaries, predictable queueing, and consistent behavior across switches, routers, WAN edges, wireless segments, and integrated communication platforms. When these pieces work together, voice traffic does not need special treatment everywhere all the time. It simply receives the right treatment when it matters most.
FAQ
Is QoS priority marking the same as QoS?
No. Priority marking is one part of QoS. It identifies traffic classes, while the broader QoS system also includes classification, trust, queueing, scheduling, shaping, policing, and congestion management.
What DSCP value is commonly used for voice traffic?
In many standards-based enterprise voice designs, telephony media is commonly marked with DSCP EF. However, the exact policy still depends on the network design and how downstream devices are configured to honor that marking.
What is the difference between DSCP and CoS?
DSCP is a Layer 3 IP marking used across routed networks, while CoS is a Layer 2 priority value carried in 802.1Q Ethernet tags. Voice networks often use both, especially between the phone and the first switch.
Should all traffic from an IP phone be marked high priority?
No. The speech media and some signaling traffic may deserve higher priority, but management sessions, firmware updates, and generic data should not automatically receive the same treatment.
Can QoS marking fix poor voice quality by itself?
Not by itself. It helps the network make better forwarding decisions, but good call quality also depends on sufficient bandwidth, correct queueing, clean switching paths, and proper end-to-end policy enforcement.