IPv6, or Internet Protocol version 6, is the modern network-layer protocol designed to carry data across IP networks and the internet. It was developed to address the long-term limits of IPv4, especially address exhaustion, while also improving routing efficiency, auto-configuration, multicast handling, and end-to-end connectivity design. In practical terms, IPv6 is not just a larger addressing scheme. It is a newer IP framework that changes how networks assign addresses, move packets, discover neighbors, and scale connected devices.
Today, IPv6 is used in enterprise networks, carrier infrastructure, cloud platforms, mobile networks, smart devices, and public internet services. Many modern operating systems, browsers, mobile providers, and internet-facing platforms already support dual-stack or native IPv6 connectivity. For network engineers, system integrators, and IT planners, understanding IPv6 is no longer optional knowledge. It is part of current and future network architecture.
What Is IPv6 Protocol?
IPv6 is the successor to IPv4 at the internet layer. It defines how packets are addressed and forwarded from one network interface to another across interconnected networks. Like IPv4, IPv6 is connectionless and packet-based. Each packet carries source and destination addressing information, and routers forward packets hop by hop toward the destination network.
The most visible difference is address size. IPv4 uses 32-bit addresses, while IPv6 uses 128-bit addresses. That change dramatically expands the available address space and supports a far more scalable addressing model. However, IPv6 also introduces a cleaner header structure, different fragmentation behavior, improved support for multicast, built-in mechanisms for stateless address configuration, and a modernized neighbor discovery process.

IPv6 expands the address space and supports modern routing and endpoint connectivity across large-scale networks.
Why Was IPv6 Introduced?
The original internet protocol design worked extremely well, but IPv4 was created in an era when the number of connected devices was far smaller than it is today. As the internet expanded across businesses, homes, cloud platforms, industrial systems, and mobile networks, the finite IPv4 address pool became a major limitation. Network address translation helped extend IPv4's practical life, but it also added complexity to end-to-end communication, application design, troubleshooting, and large-scale service delivery.
IPv6 was introduced to solve that long-term scaling problem while modernizing several parts of IP networking. The goal was not only to provide more addresses, but also to simplify routing aggregation, reduce dependence on address-sharing workarounds, improve multicast efficiency, and support automatic addressing in a more structured way. That is why IPv6 matters in data centers, ISP backbones, mobile cores, IoT deployments, campus networks, and internet-facing services.
How Does IPv6 Work?
At a basic level, IPv6 works the same way all IP protocols do: a source device creates a packet, gives it a destination address, and sends it toward a local router or directly to the destination if it is on the same link. Routers examine the destination prefix and forward the packet toward the next hop until it reaches the destination network.
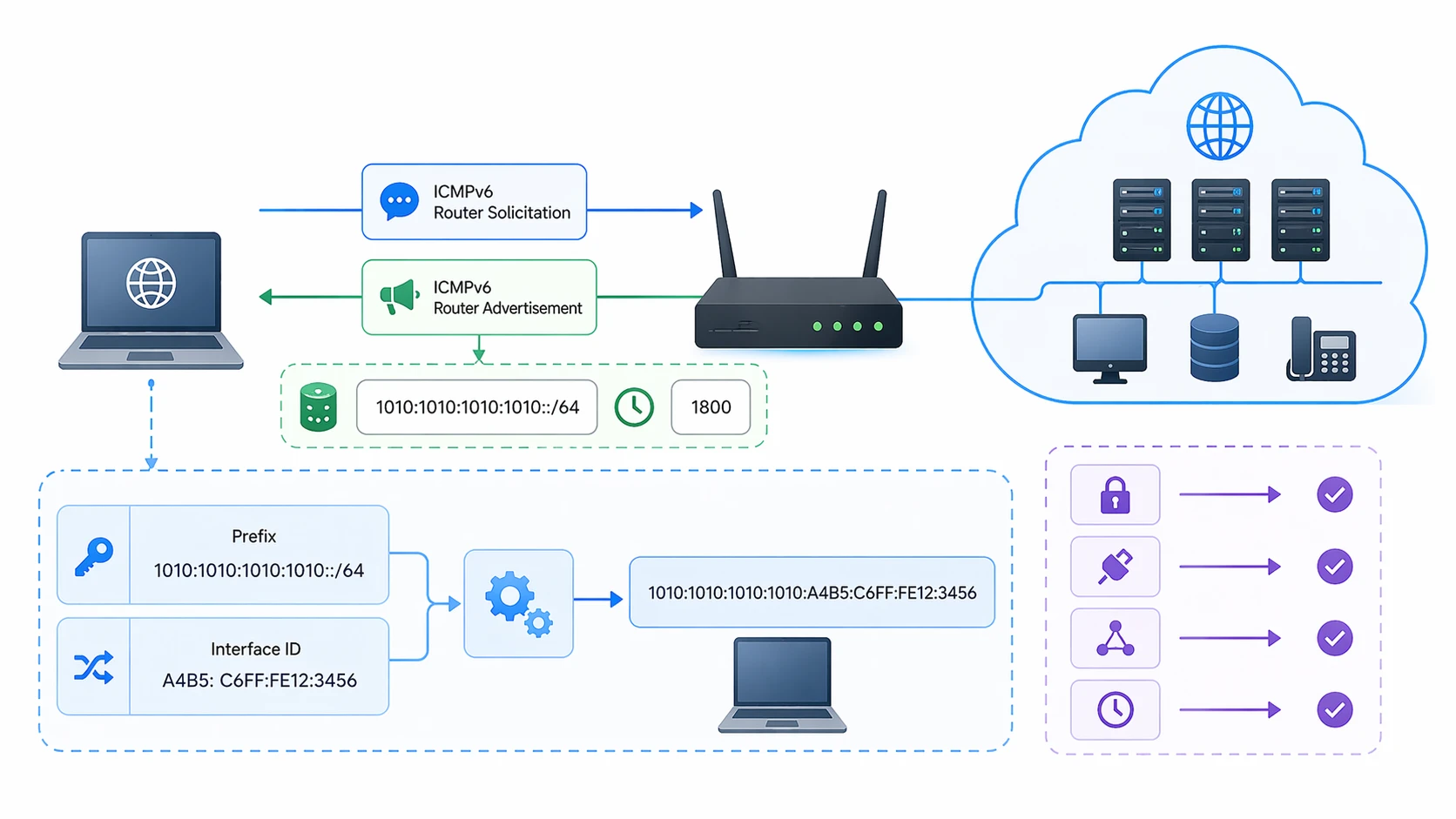
The operational flow becomes more interesting when you look at how IPv6 endpoints obtain addresses and communicate on the local link. IPv6 commonly uses link-local addresses, router advertisements, and neighbor discovery to help hosts identify local routers, generate usable addresses, and resolve Layer 2 neighbors without relying on ARP. In many deployments, a host can join a network and self-configure an address through SLAAC, while DHCPv6 may still be used for additional settings or policy-driven address management.
Core IPv6 Communication Process
A simple IPv6 communication flow usually looks like this:
- The host brings up a link-local address on its interface.
- The local router sends router advertisements with prefix and configuration information.
- The host forms a usable IPv6 address through SLAAC or receives one through DHCPv6.
- The host uses Neighbor Discovery to identify local neighbors and gateways.
- The packet is forwarded based on IPv6 routing tables until it reaches the destination network.
IPv6 Address Structure and Address Types
IPv6 addresses are written as eight groups of hexadecimal values separated by colons. Because 128 bits would be too long to read in full every time, IPv6 uses a compressed text format that allows omission of leading zeros and, in specific cases, compression of contiguous zero blocks. This makes long addresses manageable in configuration and documentation, even though they remain much longer than IPv4 addresses.
IPv6 supports three main address categories: unicast, anycast, and multicast. Unicast identifies one interface. Anycast allows the same address to be assigned to multiple interfaces so that the packet is delivered to one of them, typically the nearest according to routing. Multicast is used to send traffic to multiple interested receivers and plays a far more central role in IPv6 than broadcast did in IPv4. Traditional broadcast is not used in IPv6 in the same way.
| Address Type | Purpose | Typical Example |
|---|
| Unicast | Identifies a single interface | Global unicast or link-local address |
| Anycast | Identifies one of multiple interfaces | Used in resilient or geographically distributed services |
| Multicast | Identifies a group of receivers | Neighbor Discovery and group-based delivery |
Common IPv6 Address Classes in Practice

IPv6 forwarding remains packet-based, but addressing, local discovery, and configuration behavior differ from IPv4.
IPv6 Header and Packet Design
One of IPv6's practical improvements is a simplified base header. Unlike IPv4, the IPv6 base header is fixed in length, which helps streamline forwarding decisions. Optional information is placed in extension headers instead of being packed into a variable header structure. This design separates core forwarding information from optional features and contributes to cleaner protocol processing.
IPv6 also changes fragmentation behavior. In IPv4, routers can fragment packets in transit. In IPv6, intermediate routers do not fragment packets the same way. Instead, endpoints are expected to rely on path MTU behavior and perform fragmentation at the source when necessary. That shifts responsibility away from transit routers and supports more predictable forwarding.
Important IPv6 Header Fields
- Version: Identifies the packet as IPv6.
- Traffic Class: Used for packet handling and differentiated treatment.
- Flow Label: Supports identification of packet flows in specific scenarios.
- Payload Length: Indicates the length of the payload following the base header.
- Next Header: Identifies the following extension header or upper-layer protocol.
- Hop Limit: Similar in purpose to IPv4 TTL, preventing endless forwarding loops.
IPv6 was designed to be more than an address expansion project. Its packet format, auto-configuration model, and neighbor mechanisms reflect a broader architectural cleanup.
Neighbor Discovery, SLAAC, and DHCPv6
In IPv4, local address resolution is closely associated with ARP. IPv6 replaces that function with Neighbor Discovery, which operates using ICMPv6 messages. Neighbor Discovery supports tasks such as router discovery, address resolution, prefix discovery, reachability checks, and duplicate address detection. This makes it central to day-to-day IPv6 operation on local links.
SLAAC, or Stateless Address Autoconfiguration, is one of IPv6's most practical features. It allows a host to generate its own address from advertised network information without requiring a full stateful address assignment process. That reduces deployment friction in many environments. DHCPv6 is still important, especially where administrators want structured address assignment, policy control, or additional network parameters. In real networks, it is common to see SLAAC and DHCPv6 used in complementary ways rather than as mutually exclusive options.
IPv6 Network Architecture and Deployment Models
IPv6 can be deployed in multiple ways depending on the environment. In enterprise and service-provider networks, one of the most common strategies is dual-stack deployment, where IPv4 and IPv6 run in parallel. This allows systems and services to support both protocols during a migration period. It is often the safest operational model because it maintains compatibility while organizations gradually update applications, monitoring systems, and security controls.
Other environments may use IPv6-only segments with translation or proxy mechanisms for legacy IPv4 access. This is common in some mobile and cloud environments where address efficiency and simplified scaling are important. Tunneling and transition mechanisms may also appear in certain migration phases, though most long-term designs prefer native IPv6 wherever possible.
Typical IPv6 Architecture Layers
- Endpoints: PCs, smartphones, IP phones, IoT devices, servers, and industrial systems.
- Access Layer: Switches, Wi-Fi, and local routing points that deliver prefixes and local connectivity.
- Distribution/Core: Routers and Layer 3 infrastructure forwarding IPv6 traffic between segments.
- Security Edge: Firewalls, policy gateways, and monitoring platforms that understand IPv6 traffic.
External Connectivity: ISPs, cloud platforms, VPN edges, internet exchanges, and public-facing services.
Dual-stack deployment remains one of the most common ways to introduce IPv6 without breaking IPv4 service continuity.
Benefits of IPv6
IPv6 offers much more than a larger address pool. The expanded address space enables cleaner hierarchical planning, which helps large networks scale more naturally. It also reduces pressure to overload private addressing and NAT in every design. In environments with many devices, sites, or services, that can simplify architecture and long-term growth planning.
IPv6 also supports more efficient multicast usage, stronger alignment with modern auto-configuration methods, and cleaner packet processing models. It does not automatically make every network faster or safer, but it provides a better long-term foundation for internet-scale connectivity. When deployed well, it can reduce design compromises and improve address management flexibility.
Practical Benefits Often Seen in Real Networks
- Much larger address capacity for internet growth and device expansion.
- Better support for hierarchical addressing and route aggregation.
- Reduced dependence on address-sharing workarounds.
- Modern host auto-configuration options through SLAAC and DHCPv6.
- Cleaner multicast and neighbor management behavior.
- Stronger long-term readiness for cloud, carrier, IoT, and mobile environments.
Common Uses and Applications of IPv6
IPv6 is now used in a wide range of network scenarios. Public websites and cloud platforms use it to provide internet-facing reachability. Mobile carriers use it to support growing subscriber bases and large-scale packet-core architectures. Enterprises use it in campus networks, remote sites, and internet access designs. Data centers and cloud-native systems increasingly treat IPv6 as a first-class protocol rather than a future feature.
In industrial and communications environments, IPv6 can be relevant for IP telephony, video systems, gateways, edge controllers, remote devices, and distributed infrastructure. Its large address space and clean subnetting model are especially useful in large deployments with many endpoints, segments, or geographically distributed nodes.
Representative Application Scenarios
- Enterprise networks: Campus access, branch interconnection, internet breakout, and future-ready addressing plans.
- Cloud and data centers: Large-scale service exposure, automation, container and virtualized workloads.
- Mobile communication: Subscriber growth, packet data services, and simplified large-scale addressing.
- IoT and smart infrastructure: Sensors, controllers, gateways, and distributed device fleets.
- Public internet services: Websites, APIs, DNS, CDN edges, and globally reachable applications.
- Industrial IP systems: IP PBX, SIP devices, video surveillance, dispatch platforms, and remote monitoring nodes.
IPv4 vs IPv6: What Really Changes?
The easiest summary is that IPv4 and IPv6 both deliver packets, but they do so with different addressing scale and different operational assumptions. IPv4 remains everywhere, but its address scarcity has shaped decades of network design. IPv6 was created to remove that long-term bottleneck and to modernize how hosts and routers interact.
Operationally, IPv6 changes address length, textual notation, local discovery, packet header structure, fragmentation behavior, and the role of multicast. It also changes how network teams think about subnetting, security policy, logging, and service exposure. That is why IPv6 adoption is not only a protocol upgrade but also an operational transition.
| Area | IPv4 | IPv6 |
|---|
| Address Length | 32-bit | 128-bit |
| Broadcast | Used | Not used in the same way; multicast is preferred |
| Local Resolution | ARP | Neighbor Discovery via ICMPv6 |
| Header | Variable-length base header | Fixed-length base header with extension headers |
| Fragmentation | Routers may fragment | Source handles fragmentation; routers do not fragment in transit |
Deployment Considerations and Common Challenges
Moving to IPv6 is not simply a matter of enabling a checkbox. Real deployments require coordinated planning across routing, DNS, security policy, monitoring, logging, application behavior, firewall rules, and staff familiarity. A network can be partially IPv6-capable and still fail operationally if tools, ACLs, VPNs, or upstream services are not ready.
One of the most common mistakes is treating IPv6 as irrelevant because IPv4 still works. In reality, many operating systems and applications will prefer IPv6 when available. That means an incomplete or poorly secured IPv6 environment can create blind spots. Mature deployment requires the same discipline applied to IPv4: addressing plans, segmentation, routing policy, access control, and visibility.
Useful Deployment Checklist
- Create a structured IPv6 addressing plan before broad rollout.
- Verify router, firewall, VPN, SBC, and monitoring support for IPv6.
- Review DNS behavior, especially AAAA records and dual-stack resolution.
- Test applications, portals, APIs, and management systems in dual-stack conditions.
- Apply IPv6-aware security policy instead of assuming IPv4 rules are enough.
- Train operations teams to troubleshoot Neighbor Discovery, prefixes, and routing behavior.
Frequently Asked Questions
Is IPv6 replacing IPv4 completely?
IPv6 is intended as the long-term successor to IPv4, but in most real environments the transition is gradual. Dual-stack operation remains common because many networks and applications still need IPv4 compatibility.
Does IPv6 automatically improve security?
No. IPv6 supports modern security architectures, but it does not automatically make a network secure. Firewalls, segmentation, access control, visibility, and secure configuration are still essential.
Is IPv6 faster than IPv4?
Not by definition. Performance depends on network paths, provider support, application behavior, and infrastructure quality. In some cases IPv6 can perform better, but the protocol itself does not guarantee faster communication.
What is the main reason organizations deploy IPv6?
The biggest reason is long-term scalability. IPv6 provides a much larger address space and supports cleaner addressing for growing networks, cloud systems, mobile users, and large device populations.
Can IPv6 work with existing enterprise systems?
Yes, but compatibility must be verified. Routers, firewalls, IP phones, gateways, cameras, servers, management platforms, and security tools all need to be checked for IPv6 readiness.
Conclusion
IPv6 is the modern internet protocol foundation for large-scale IP networking. It expands addressing from 32 bits to 128 bits, but its significance goes beyond that. IPv6 changes local discovery, streamlines header design, supports structured auto-configuration, and gives networks a more sustainable way to grow. For enterprises, carriers, cloud platforms, and industrial IP systems, IPv6 is not just a future topic. It is already part of the current networking landscape.
The most effective way to understand IPv6 is to stop viewing it as a bigger address label and start viewing it as a modern operational framework for IP communication. Once you see that difference, its uses, architectural value, and practical applications become much clearer.